The Catcalling Experiment
Alissa and I worked together for this social breaching experiment. We decided to “catcall” males to try to make them uncomfortable after the experiences we have both had. We wanted to do a breaching experiment that focused on switching gender roles because we are both interested in studying these norms.
The work was performance based and reminds me of other performance pieces by artists who also experiment with these themes in their work.
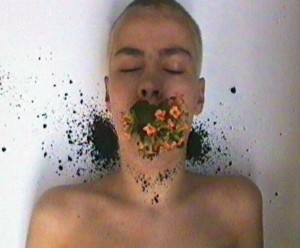
Ene-Liis Semper is an artist whom I know from seeing her video at the Museum of Fine Arts in Boston. It was titled Oasis and presents herself acting as the ground of the Earth. In other words, the film is an aerial view of her mouth and her partner feeds soil and a flower into the opening and then plants a flower. She wanted to explore stereotypical femininity and “women’s work,” which can be explained as gardening. Her piece results in presenting an “extreme display of forced femininity.” While the work Alissa and I created was the complete switching of gender roles, I still believe that they tread the same water and are important in exploring the prevalent issues in modern day society.
Another artist that I respond to strongly is Marina Abramovic. I bring her up because I think vulnerability is a constant theme in her work, and I felt like the catcalling breach embodied vulnerability. Rhythm 0 is a performance based piece by Abramovic that really focuses on these particular themes. In this art work, she stands naked in a gallery space and provides a table of random objects that the audience is allowed to use on her in any way they please. The objects range from a handgun, to a rose thorn, to lipstick. The audience can touch her body, harm her body, and use her in a way that creates a truly uncomfortable experience. Below is an image and further explanation of her piece to get a better sense of her work.
http://www.whatevo.com/post/An-artists-interesting-social-experiment-DB34608A900CE7B3
The video of the catcalling experiment is below:
https://www.youtube.com/watch?v=03T9n66P9wE&feature=youtu.be
Alissa and I both felt very uncomfortable doing this exercise and it was hard to imagine that people are okay with doing this on a daily basis. We got disturbed looks from many of the men we catcalled which proved our point. However, what was interesting to us was that for one of the scenes in which we speak outwardly to a male and his friend, they later came back to sit next to us and eat their lunch. We were taken aback by this action, and after discussing it after, we decided we would not have gone to eat next to two males who were speaking out to us. It is then important to consider gender roles and how different genders act in certain situations.
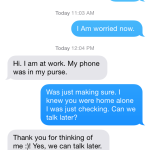
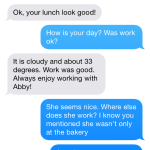
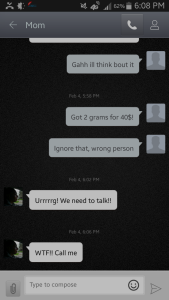
What I thought was interesting was how this breach differed from the technology mediated breach. There is something very different about “breaking the rules” with no barrier, meaning a mobile device or computer. Without these objects in between the target and the instigator, it creates a very forward, vulnerable experience. The tech mediated breach didn’t require any face to face contact. There was a level of safety and comfort in being able to hide behind these machines rather than standing in the open, showing our faces and speaking to these men.
Catcalling on the streets of a city in comparison to making comments on someone’s photo online is interesting to discuss here. The two differ completely and the outcomes are different as well. Online, there is a sense of safety as mentioned before, but it also allows the one targeted to ignore what has been said, or “delete it.” On the streets, the person being targeted can still ignore, but it is much more direct and you cannot backspace the situation. It has been done and you simply cannot erase that.
A good example to bring up that relates to these ideas is the plot of the article Here Comes Everybody by Clay Shirky. The article explains a situation in which a man tries to get his friend’s phone back for her. He does this by starting a site on the Internet. He even talks to the person who stole the phone through the online platform. This is very different than going to the person’s house and confronting them face to face.
Overall, I think social breaching experiments are important to explore and I think it is healthy to break social norms and see the reactions of the public. Without these exercises, we will always be living in the confines of a society without ever breaking down the walls and seeing how we can change things for the better.