Author Archive
Week 6 reading
The Internet of Things is a complex topic and after a fair amount of research and thinking I’m still not sure I know enough to talk about it. I am a fan of gadgets and interconnected things, I was really excited for the Chromecast and enjoyed using it immensely for those first few weeks. I watch a fair amount of youtube videos, anime, and streaming tv shows and instead of buying a costly “smart tv” I could purchase a $30 dongle that works with any HDMI port. For some shows that weren’t available for streaming I would have to hook up a laptop to the tv and try to balance it somewhere nearby, and the Chromecast offered an alternative. Until I realized that interference from other networks and the hidden position of the dongle itself were giving me painfully slow streaming speeds it was a magnificent gadget.
The adaptable and portable connector is one of the parts of the “Internet of things” that I look forward to. When you start to embed connectivity into things, and black box their settings and interface from the consumer I start to question the value or intent behind it. Not only do you run into compatibility issues with different companies defining their own standards, but the designed automation can lead to negative consequences for the consumer. In Sara Watsons thought experiment on the Internet of Paternalistic things, the device network seeds doubt in the woman’s mind, and restricts her agency in her own life based on what could be faulty information. Computers, especially when networked, are prone to minor malfunctions or miscommunication. When we give this technology control over parts of our lives we suffer real consequences instead of having to refresh a webpage or reboot.
Even if that was the only risk involved in the technology behind the “Internet of Things” it would cause me concern. The secondary issue to me is the physical devices themselves. In the current western model, multiple devices are pushing for dominance. A consumer looking to “live the dream” marketed to them would have to buy a variety of products to fill their automated houses. Companies could enforce brand loyalty by only allowing their products to work with select partners or their own products. On the hardware side, battery and wireless network infrastructure are not capable of fully handling the increased load of multiple devices. Frequency interference and constant recharging would slow down processes that would be instantaneous if they didn’t require a network connection. An example of this can be seen in EA game’s launch of Sim City, where they required users to connect to their online servers to play a single player game that has no need for a network. On launch day, a large portion of their customers were not able to play the game because their servers couldn’t handle the load.
Privacy is another issue with the “Internet of Things” and even in its formative years these technologies are pushing towards redefining personal property and marketing tactics through collecting personal information. LG and Samsung have recently been noticed for some major privacy concerns with their smart tvs. These smart tv’s often are designed to consistently send usage statistics to their home companies or 3rd parties for targeted advertisement. In 2013, it was found that some would send the file and folder names of shared folders on the home network and on connected usb drives. If it wasn’t strange enough that they would gather all the personal files connected to them, they sent them to their companies in unencrypted plaintext. More recent devices would include a microphone for voice commands, but it was not always clear when it was listening. And in order for the voice to be converted to text, the recordings are sent to a third party company, often with poor encryption or with little to no notification from the tv company. These devices even cause problems for people aware of their security issues, as these tracking services are touted as “opt in”, but refusing to accept them disables most if not all of the smart content. So these companies are selling products to consumers, but disabling features if the consumer does not agree to their ever-changing contracts.
Now I have many concerns with these devices, but I do see their value. People enjoy things that simply work, or that remember and process information for them. The use of RFID tags in Disney World is what I think a positive example of this technology working. Constant tracking and data-mining are not a concern to me in that context because of the space and intent they are contained in. For a vacation destination having peace of mind is a great goal, and in order to be tracked you need to be on the premises of the park. Amusement parks are a great controlled environment, and with so many people coming and going, the tracking technology allows the staff to provide personalized services and experiences without placing enormous strain on employees. And RFID as a means of locative tracking is great, since it has a limited range. Unlike internet and gps tracking it is more of an “on or off” with each sensor you approach. It serves more as a means of announcing you are entering an area than a means of surveillance.
My ideal for the “Internet of things” would require many changes in our society. Tech literacy, so people could have agency in what their devices do or to create their own. Privacy reform, so privacy is not treated as a sign of something to hide but as a right to control your own life. Infrastructure improvement, so that the electricity and network throughput to use these devices is available, and so their cost may be brought down to affordable ranges for the majority of the population. My belief is that these changes will probably not occur before the technology reaches consumer markets, so it will probably be trail by fire for the “Internet of Things.”
Exercise 4, no Google
I went through the week with only a few slip-ups on not using Google services. My desktop still had Chrome as default browser so links would open up in it, I closed the page before it loaded but I never got around to changing default so it happened a few times. I didn’t watch any youtube videos even though all of the embedded videos on reddit were youtube. I had to go without alot, leaving large chunks out of my usual internet surfing regimen.
I did have to intentiionally use Gmai and Google Docs yesterday, as my group for Gameplay and Performance uploaded some necessary files to Google Drive. I had to get the link from Gmail and go to the doc to download it, but we were pressed for time and it was easier than getting in contact with the original file creator and having them email me.
During this week I used Firefox primarily and noticed some new things about it. It loads slower than Chrome overall, and on my small tablet it will often crash the entire page. Unlike Chrome it uses a separate Flash plugin container to run most media and videos (non youtube included). This means its memory usage spikes and with the limited RAM on my tablet it would cause the window to go black even though the media would still play. Chrome also apparently runs in the background unless you tell it that it can’t, which is terrifying. Chrome often disperses its running processes while Firefox keeps it all in one container. This distribution probably explains the performance difference between the two browsers across various devices, but the way Chrome can run so many things simultaneously and in the background is unnerving. I also forgot to download firefox on my android phone before the time period began, so I couldnt use any browser on my phone for a week, which was difficult.
Overall this week was mostly just an inconvenience. I’ve already been suspicious of Google products and kept track of what was running on my devices, but finding out about the background processes on windows 8.1 was surprising and a valuable experience.
Exercise 3
“Want me to talk about how much I hate Facebook?”
For Exercise 3 I interviewed my mother, Maureen. Here is the audio recording:
[soundcloud url=”https://api.soundcloud.com/tracks/190786179″ params=”color=ff5500&auto_play=false&hide_related=false&show_comments=true&show_user=true&show_reposts=false” width=”100%” height=”166″ iframe=”true” /]
My mother worked for IBM from 1982 to 1998, then at AT&T until present day. She started as a secretary for the creators of the internal IBM network, the Corporate Consolidated Data Network. Then she worked for the helpdesk of that network. Since then she has been managing corporate accounts and was a salesperson for a short while. She started out when users had to open up a new Terminal for each application they ran, and personal computers were a security risk to the emerging corporate network. She now will often work from home, since few of her coworkers are local and the office space is underused. She can now remote connect to the corporate network from her laptop, cellphone or tablet.
While interviewing my mother if found that she had some opinions about communications technology that aligned with those of Sherry Turkle. She really prefers to talk to someone over the phone so she can hear their tone. She works with technology but as a manager or salesperson she finds it important to connect or understand the person on the other end of the communication in order to complete the job. She feels frustrated about Facebook communications, because it is impossible to tell the tone or subtext in a written comment on someone’s wall or photo. She is also “on call” almost around the clock, especially when working with people around the world. I’ve heard her get up at 6 or 7 to make a phone call to the other side of the world where it is long after business hours, and the people on both end of the call are tired and frustrated. She recently purchased a new Bluetooth headset for her cellphone; it’s a headset that can rest around your neck and vibrate when you receive a call. Since it doesn’t need to be in your ear when not in use, it is more comfortable and harder to misplace than her previous devices. Right after she explained it to me is said, “…so it’s a collar?” and she laughed but I knew it slightly changed her opinion on her shiny new device. In Postscript on Societies of Control Deleuze perfectly described this device before it even existed. “The conception of a control mechanism, giving the position of any element within an open environment at any given instant (whether animal in a reserve or a human in a corporation, as with an electric collar), is not necessarily one of science fiction.” She often had conflict with the systems of access that plague the control society. If a technical or network issue prevents her from running the secure programs that connect her to the corporate network, she cannot work. She needs to be logged in to access email and passwords that would allow her to log in to other phone calls or work services. And if the issue arrives, she must either travel into the office to connect physically to the network, or she must turn over control to technical support who have access to administrator privileges on the computer she uses every day. As she mentions in the interview, she spends all of her day on the computer, so she wants to spend her free time offline but often can’t.
Her primary social media platform is Facebook. She is the third of 8 brothers and sisters who are spread along the East coast from Maine to Virginia. In order to keep up to date with the family, she relies on Facebook and phone calls. Often, a post on Facebook will be the impetus for her to call someone and start a conversation. However Facebook’s gradual increase in advertising content is causing frustration and interferes with the social aspect of the network. As mentioned in both the Theory of Everything and RadioLab podcasts, Facebook and other social media platforms are simultaneously experimenting with and selling this focused access to users. By logging and analyzing the choices made on a screen, they have not only evolved their methods of how users report embarrassing photos but also how they structure their advertising on the page. Rather than the intrusive pop-up ad they mix in advertisements as “suggested posts” along with the standard banner ads on the side of the page.
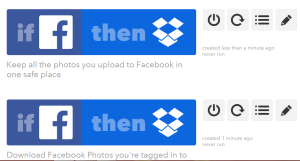
So in an effort to catalog and store all the important photos she posts and is tagged in on Facebook, I used IFTTT to link her Facebook to Dropbox. I had her setup her own account on IFTTT in case she wants to modify or add to her recipes, or in the event that she shifts to a new social media platform and wants to automate something in relation to Facebook. She would like it if her family found and moved to a new platform that wasn’t so focused on advertising, or often riddled with negativity. Hopefully this automated download process will assist in that by storing her photos in an alternate location so the leave from Facebook can be swift and easy.
Exercise 2 twitter breaching
For my technological social breach I decided to use twitter, since it was a platform I had little experience with but was somewhat aware of how it worked. I set up a simple bot using IFTTT, and connected it to a Twitter account I set up @BottingtonC. BottingtonC tracks things like my location, text msging, and likes on reddit and posts them in the vein of surveillance. Instead of tweeting to update people about my day, this surveillance bot tweets for me automatically. I’m breaching the use of twitter as a platform to follow others and gain followers, instead it is only following me. A detailed stream of location updates and tweets can be used to track someone, but in this case its the only use.
I also made an additional twitter account, @solitary_follow name “Only Follower” I had planned to automate it to find users with no followers and follow them, but stop following if they gained other followers. The automation proved difficult, as there is no way to search for people based on how few followers they have or how recently they made their accounts. So I decided to start out doing it myself, by searching for most recent tweets with “first tweet ever” and clicking each name to see who had 0 followers.
The intent of this account is to invert twitters ingrained system of focusing on popular accounts, while also potentially annoying people by pointing out their lack of followers. Is it better to have no followers or a solitary follow?
Week 3 reading
Summary: